Little Known Questions About Risk Management Enterprise.
Table of Contents5 Simple Techniques For Risk Management Enterprise10 Simple Techniques For Risk Management EnterpriseThe Best Strategy To Use For Risk Management EnterpriseAll about Risk Management EnterpriseRisk Management Enterprise - An Overview4 Simple Techniques For Risk Management EnterpriseThe Only Guide to Risk Management Enterprise
Below are some of its crucial functions that facilities should understand. So, take a look. Real-Time Danger Analyses and Mitigation in this software application enable organizations to continuously check and evaluate dangers as they advance. This function leverages real-time information and computerized analysis to determine potential threats immediately. As soon as threats are determined, the software assists in prompt mitigation actions.
They attend to the difficulty of ongoing risk administration by offering devices to check risks continually. KRIs enhance security threat oversight, making sure that potential dangers are determined and taken care of properly.
The Definitive Guide to Risk Management Enterprise
IT run the risk of monitoring is a part of venture danger administration (ERM), made to bring IT risk in line with a company's threat hunger. IT run the risk of monitoring (ITRM) encompasses the policies, treatments and modern technology needed to minimize risks and vulnerabilities, while keeping compliance with suitable regulative needs. In enhancement, ITRM looks for to limit the consequences of devastating events, such as safety and security breaches.
While ITRM frameworks supply valuable assistance, it's very easy for IT teams to deal with "structure overload." Veronica Rose, ISACA board supervisor and an information systems auditor at Metropol Corp. Ltd., recommends making use of a mix of frameworks to attain the very best outcomes. For instance, the ISACA Danger IT structure aligns well with the COBIT 2019 framework, Rose stated.
Venture Risk Management Software Application Advancement: Advantages & Features, Cost. With technical innovations, threats are continually increasing. That being claimed, organizations are more probable to deal with challenges that impact their finances, operations, and online reputation. From quickly changing markets to regulatory adjustments and cyber threats, organizations navigate via a constantly altering sea of risks.
9 Simple Techniques For Risk Management Enterprise
In this blog, we will study the world of ERM software application, exploring what it is, its advantages, attributes, etc so that you can build one for your company. Venture Threat Management (ERM) software is the application program for planning, directing, arranging, and controlling company tasks and simplifying danger monitoring processes.
With ERM, companies can make informative choices to boost the total strength of the company. Read: ERP Application Advancement Devoted ERM systems are critical for businesses that regularly deal with large quantities of delicate info and multiple stakeholders to authorize strategic choices. Some sectors where ERM has actually ended up being a common system are healthcare, finance, building and construction, insurance, and infotech (IT).
: It is demanding for any business to undergo an in-depth audit. It can be stayed clear of by making use of the ERM software program system. This system automates law compliance monitoring to maintain the organization safe and secure and certified. Various other than that, it also logs and categorizes all the documents in the system making it easier for auditors to evaluate processes much faster.
The 5-Minute Rule for Risk Management Enterprise
You can likewise attach existing software application systems to the ERM using APIs or by including data manually. Businesses can utilize ERM to evaluate threats based upon their possible influence for better risk monitoring and mitigation.: Adding this attribute enables users to get real-time alerts on their gadgets about any risk that may take place and its impact.

Rather, the software allows them to establish limits for various procedures and send press notices in instance of possible threats.: By incorporating data visualization and reporting in the custom ERM software application, companies can obtain clear insights about danger trends and performance.: It is required for companies to abide by industry conformity and regulatory criteria.

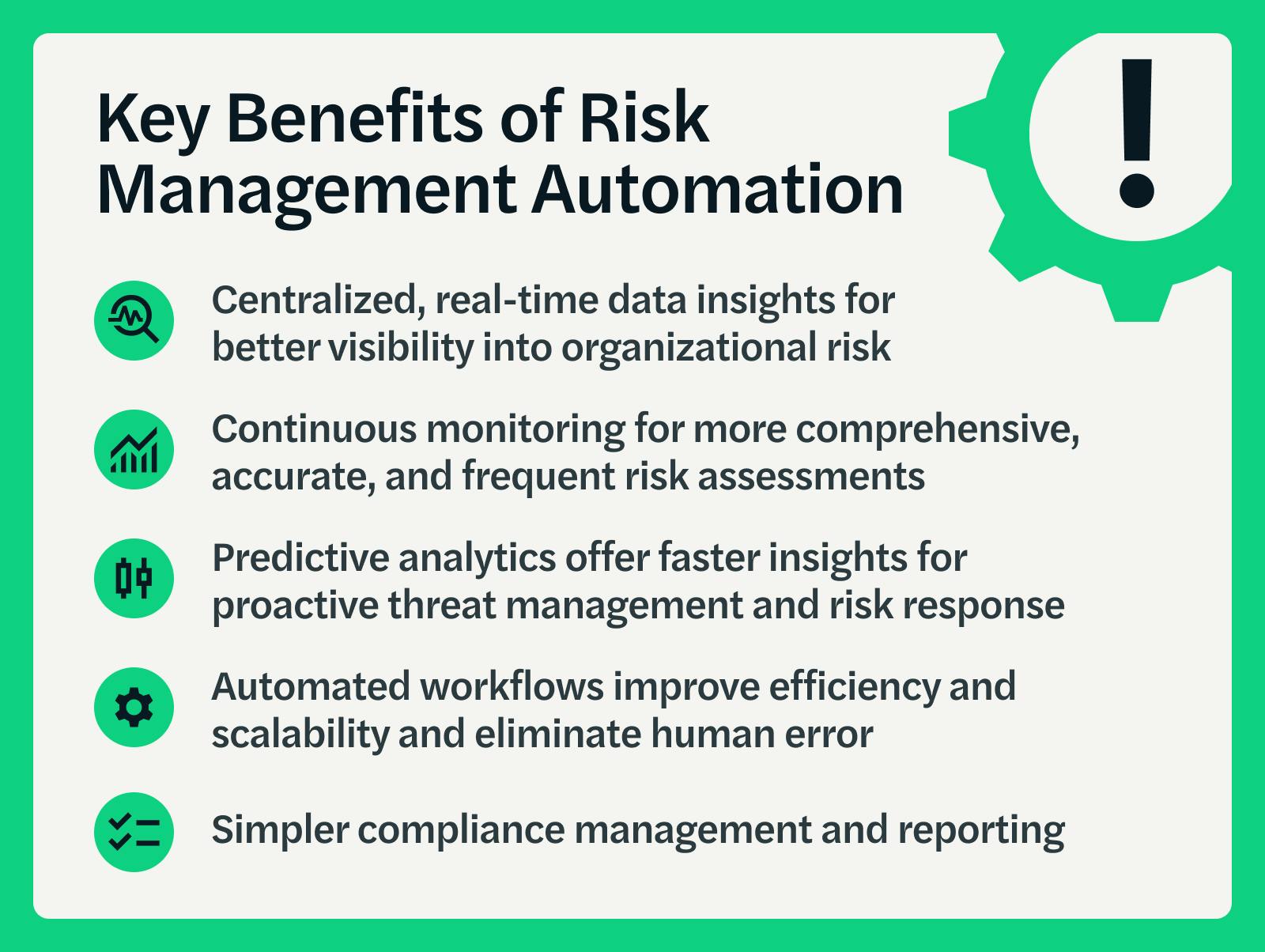
These systems make it possible for firms to execute best-practice danger management procedures that align with sector criteria, providing a powerful, technology-driven approach to determining, evaluating, and mitigating risks. This blog discovers the advantages of automatic risk monitoring tools, the areas of threat administration they can automate, and the worth they give a company.
Our Risk Management Enterprise PDFs
Groups can set up kinds with the that site relevant fields and conveniently produce different forms for various risk kinds. These risk evaluation kinds can be circulated for completion via automated operations that send notifications to the pertinent personnel to complete the types online. If types are not finished by the deadline, then chaser emails are automatically sent out by the system.
The control monitoring and control testing procedure can likewise be automated. Companies can make use of automated process to send regular control examination alerts and personnel can get in the outcomes via on-line forms. Controls can likewise be kept track of by the software by setting policies to send out notifies based on control data held in other systems and spread sheets that is pulled into the platform by means of API combinations.
Risk Read More Here monitoring automation software can also support with threat reporting for all levels of the business. Leaders can watch records on danger exposure and control effectiveness with a selection of reporting outcomes including fixed reports, Power BI interactive records, bowtie evaluation, and Monte Carlo simulations. The capacity to pull actual time reports at the touch of a button cuts out tough information adjustment tasks leaving risk groups with more time to assess the information and advise business on the very best course of action.
The demand for effective has never been much more pressing. Risk Management Enterprise. Organizations operating in affordable, fast-changing markets can't afford delays or inadequacies in dealing with prospective risks. Standard danger management making use of hands-on spreadsheet-based processes, while acquainted, typically cause fragmented information, time-consuming reporting, and an increased probability of human error. Automating the danger management procedure with software application addresses these drawbacks.
The Only Guide to Risk Management Enterprise
This makes certain threat signs up are always existing and straightened with business purposes. Conformity is an additional essential vehicle driver for automating risk monitoring. Specifications like ISO 31000, CPS 230 and COSO all offer advice around danger monitoring best methods and control frameworks, and automated threat administration devices are structured to align with these demands helping companies to meet most generally used risk monitoring criteria.
Search for risk software systems with a permissions hierarchy to conveniently establish operations for danger escalation. This functionality enables you to customize the view for each individual, so they only see the data relevant to them. Ensure the ERM software application supplies user monitoring so you can see who entered what information and when.
Look for out devices that offer job risk monitoring abilities to manage your jobs and profiles and the linked risks. The advantages of adopting risk administration automation software expand far past performance.
The Greatest Guide To Risk Management Enterprise
While the instance for automation is compelling, executing a danger administration system is not without its difficulties. To conquer the challenges of risk administration automation, companies need to invest in information cleansing and governance to guarantee a solid structure for implementing an automated system.
Automation in threat monitoring equips services to transform their technique to take the chance of and build a stronger foundation for the future (Risk Management Enterprise). The question is no longer whether to automate risk administration, it's just how quickly you can begin. To see the Riskonnect in action,
The solution frequently depends on exactly how well dangers are prepared for and taken care of. Task management software application serves as the navigator in the troubled waters of job implementation, offering tools that recognize and examine dangers and devise strategies to mitigate them effectively. From real-time information analytics to thorough danger surveillance control panels, these devices provide a 360-degree sight of the job landscape, making it possible for job managers to make enlightened decisions that maintain their projects on the right track and within spending plan.